Ipsec Pre Shared Key Psk Generator
The role of preshared key (or certificate) is to authenticate the other peer. Even if connection is encrypted, you need to know that the peer you are establishing connection with is the one it should be. Encryption provides confidentiality in the connection and preshared key that only you and the other party knows provides the authentication. A pre-shared key (PSK) or shared secret is a string of text a VPN (virtual private network) or other service expects to get before it receives any other credentials (such as a username and password). Microsoft Windows calls this string the 'pre-shared key for authentication', but in most operating systems it is known as a 'shared secret'. Some WPA-PSK user interfaces (such as the one in Windows XP) allows the 256-bit WPA pre-shared key to be directly provided as 64 hexadecimal characters.
Contents
Introduction
Cisco IOS® Software Release 12.3(2)T code introduces the functionality that allows the router to encrypt the ISAKMP pre-shared key in secure type 6 format in nonvolatile RAM (NVRAM). The pre-shared key to be encrypted can be configured either as standard, under an ISAKMP key ring, in aggressive mode, or as the group password under an EzVPN server or client setup. This sample configuration details how to set up encryption of both existing and new pre-shared keys.
Prerequisites
Requirements
There are no specific requirements for this document.
Components Used
The information in this document is based on this software version:
Cisco IOS Software Release 12.3(2)T
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command.
Conventions
Refer to the Cisco Technical Tips Conventions for more information on document conventions.
Configure
This section presents you with the information you can use to configure the features this document describes.
Note: Use the Command Lookup Tool (registered customers only) to obtain more information on the commands used in this section.
These two new commands are introduced in order to enable pre-shared key encryption:
key config-key password-encryption [master key]
password encryption aes
The [master key] is the password/key used to encrypt all other keys in the router configuration with the use of an Advance Encryption Standard (AES) symmetric cipher. The master key is not stored in the router configuration and cannot be seen or obtained in any way while connected to the router.
Once configured, the master key is used to encrypt any existing or new keys in the router configuration. If the [master key] is not specified on the command line, the router prompts the user to enter the key and to re-enter it for verification. If a key already exists, the user is prompted to enter the old key first. Keys are not encrypted until you issue the password encryption aes command.
The master key can be changed (although this should not be necessary unless the key has become compromised in some way) by issuing the key config-key.. command again with the new [master-key]. Any existing encrypted keys in the router configuration are re-encrypted with the new key.
You can delete the master key when you issue the no key config-key... However, this renders all currently configured keys in the router configuration useless (a warning message displays that details this and confirms the master key deletion). Since the master key no longer exists, the type 6 passwords cannot be unencrypted and used by the router.
Psk Pre Shared Key
Note: For security reasons, neither the removal of the master key, nor the removal of the password encryption aes command unencrypts the passwords in the router configuration. Once passwords are encrypted, they are not unencrypted. Existing encrypted keys in the configuration are still able to be unencrypted provided the master key is not removed.
Additionally, in order to see debug-type messages of password encryption functions, use the password logging command in configuration mode.
Configurations
This document uses these configurations on the router:
| Encrypt the Existing Pre-shared Key |
|---|
| Add a New Master Key Interactively |
|---|
| Modify the Existing Master Key Interactively |
|---|
| Delete the Master Key |
|---|
Verify
There is currently no verification procedure available for this configuration.
Troubleshoot
There is currently no specific troubleshooting information available for this configuration.
Related Information
-->Azure S2S VPN connections provide secure, cross-premises connectivity between customer premises and Azure. This tutorial walks through IPsec S2S VPN connection life cycles such as creating and managing a S2S VPN connection. You learn how to:
- Create an S2S VPN connection
- Update the connection property: pre-shared key, BGP, IPsec/IKE policy
- Add more VPN connections
- Delete a VPN connection
The following diagram shows the topology for this tutorial:
Working with Azure Cloud Shell and Azure PowerShell
This article uses PowerShell cmdlets. To run the cmdlets, you can use Azure Cloud Shell. The Azure Cloud Shell is a free interactive shell that you can use to run the steps in this article. It has common Azure tools preinstalled and configured to use with your account.
To open the Cloud Shell, just select Try it from the upper right corner of a code block. You can also launch Cloud Shell in a separate browser tab by going to https://shell.azure.com/powershell. Select Copy to copy the blocks of code, paste it into the Cloud Shell, and press enter to run it.
Requirements
Complete the first tutorial: Create VPN gateway with Azure PowerShell to create the following resources:
- Resource group (TestRG1), virtual network (VNet1), and the GatewaySubnet
- VPN gateway (VNet1GW)
The virtual network parameter values are listed below. Note the additional values for the local network gateway which represent your on-premises network. Change the values below based on your environment and network setup, then copy and paste to set the variables for this tutorial. If your Cloud Shell session times out, or you need to use a different PowerShell window, copy and paste the variables to your new session and continue the tutorial.
Note
If you are using this to make a connection, be sure to change the values to match your on-premises network. If you are just running these steps as a tutorial, you don't need to make changes, but the connection will not work.
The workflow to create an S2S VPN connection is straightforward:
- Create a local network gateway to represent your on-premises network
- Create a connection between your Azure VPN gateway and the local network gateway
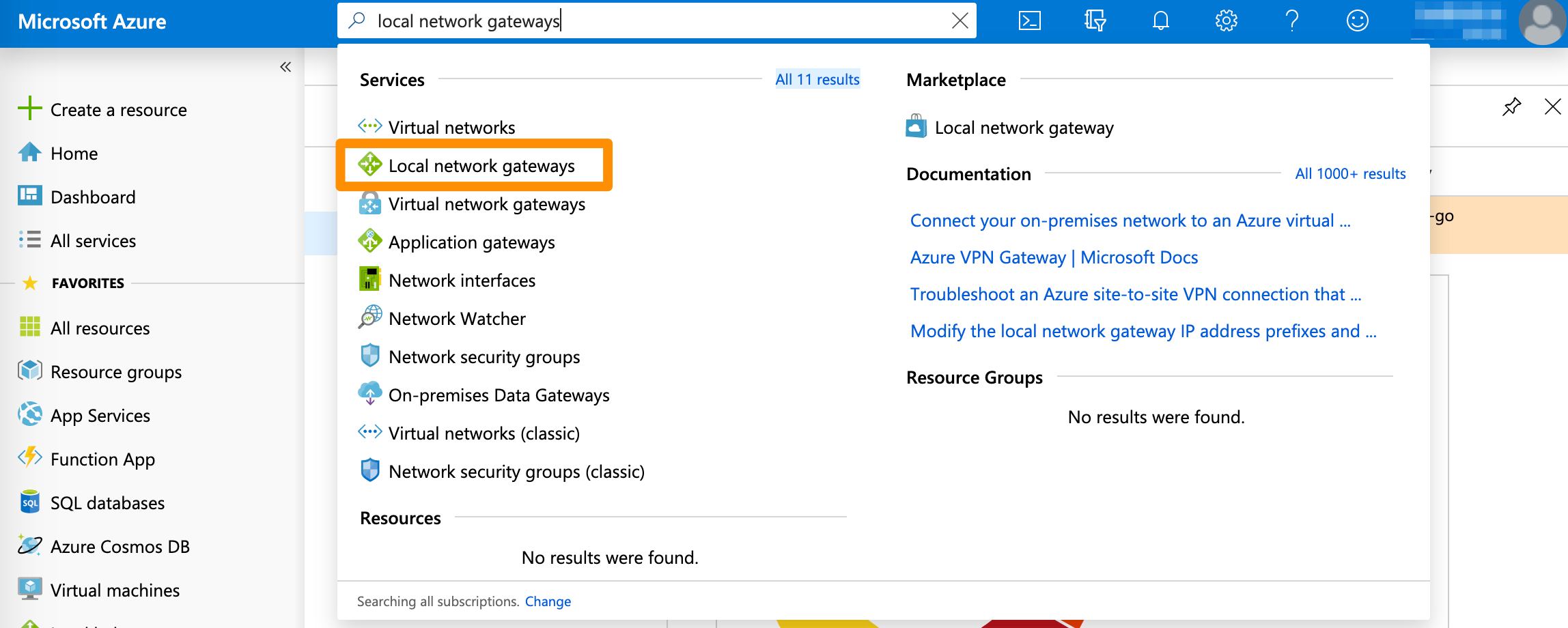
Create a local network gateway
A local network gateway represents your on-premises network. You can specify the properties of your on-premises network in the local network gateway, including:
- Public IP address of your VPN device
- On-premises address space
- (Optional) BGP attributes (BGP peer IP address and AS number)
Create a local network gateway with the New-AzLocalNetworkGateway command.
Create a S2S VPN connection
Next, create a Site-to-Site VPN connection between your virtual network gateway and your VPN device with the New-AzVirtualNetworkGatewayConnection. Notice that the '-ConnectionType' for Site-to-Site VPN is IPsec.
Add the optional '-EnableBGP $True' property to enable BGP for the connection if you are using BGP. It is disabled by default. Parameter '-ConnectionProtocol' is optional with IKEv2 as default. You can create the connection with IKEv1 protocols by specifying -ConnectionProtocol IKEv1.
Update the VPN connection pre-shared key, BGP, and IPsec/IKE policy
View and update your pre-shared key
Azure S2S VPN connection uses a pre-shared key (secret) to authenticate between your on-premises VPN device and the Azure VPN gateway. You can view and update the pre-shared key for a connection with Get-AzVirtualNetworkGatewayConnectionSharedKey and Set-AzVirtualNetworkGatewayConnectionSharedKey. Activation key generator for games.
Important
The pre-shared key is a string of printable ASCII characters no longer than 128 in length.
This command shows the pre-shared key for the connection:
The output will be 'Azure@!b2C3' following the example above. Use the command below to change the pre-shared key value to 'Azure@!_b2=C3':
Psk Generator Ipsec
Enable BGP on VPN connection
Azure VPN gateway supports BGP dynamic routing protocol. You can enable BGP on each individual connection, depending on whether you are using BGP in your on-premises networks and devices. Specify the following BGP properties before enabling BGP on the connection:
- Azure VPN ASN (Autonomous System Number)
- On-premises local network gateway ASN
- On-premises local network gateway BGP peer IP address
If you have not configured the BGP properties, the following commands add these properties to your VPN gateway and local network gateway: Set-AzVirtualNetworkGateway and Set-AzLocalNetworkGateway.
Ipsec Pre Shared Key Psk Generator Free
Use the following example to configure BGP properties:
Enable BGP with Set-AzVirtualNetworkGatewayConnection.
You can disable BGP by changing the '-EnableBGP' property value to $False. Refer to BGP on Azure VPN gateways for more detailed explanations of BGP on Azure VPN gateways.
Apply a custom IPsec/IKE policy on the connection
You can apply an optional IPsec/IKE policy to specify the exact combination of IPsec/IKE cryptographic algorithms and key strengths on the connection, instead of using the default proposals. The following sample script creates a different IPsec/IKE policy with the following algorithms and parameters:
- IKEv2: AES256, SHA256, DHGroup14
- IPsec: AES128, SHA1, PFS14, SA Lifetime 14,400 seconds & 102,400,000 KB
Refer to IPsec/IKE policy for S2S or VNet-to-VNet connections for a complete list of algorithms and instructions.
Add another S2S VPN connection
Add an additional S2S VPN connection to the same VPN gateway, create another local network gateway, and create a new connection between the new local network gateway and the VPN gateway. Use the following examples, making sure to modify the variables to reflect your own network configuration.
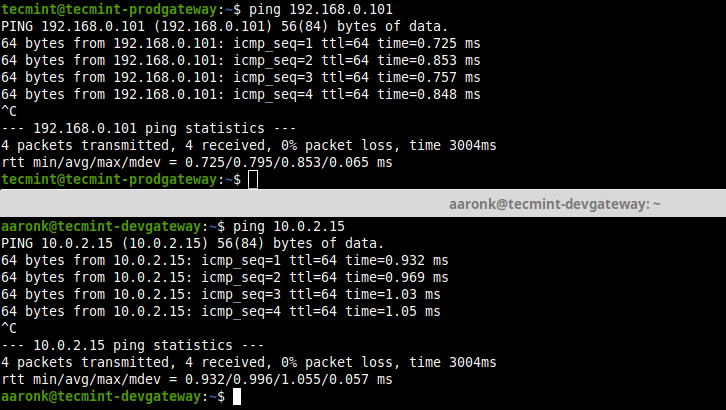
There are now two S2S VPN connections to your Azure VPN gateway.
Delete a S2S VPN connection
Delete a S2S VPN connection with Remove-AzVirtualNetworkGatewayConnection.
Delete the local network gateway if you no longer need it. You cannot delete a local network gateway if there are other connections associated with it.
Clean up resources
If this configuration is part of a prototype, test, or proof-of-concept deployment, you can use the Remove-AzResourceGroup command to remove the resource group, the VPN gateway, and all related resources.
Next steps
In this tutorial, you learned about creating and managing S2S VPN connections such as how to:
- Create an S2S VPN connection
- Update the connection property: pre-shared key, BGP, IPsec/IKE policy
- Add more VPN connections
- Delete a VPN connection
Pre Shared Key Blackberry
Advance to the following tutorials to learn about S2S, VNet-to-VNet, and P2S connections.